




The more closer we are becoming to technology and the gadgets, the more we are being faced by privacy and security issues. In the latest of such cases, the tech giant Google has also removed 13 Android apps from its offical store i.e.,Google Playstore. The move was carried by in lieu of a notification that was raised by the security researchers that these applications made unauthorized downloads to endless Android devices.
These apps had to be given root privileges and once the user gives it, these applications without informing or notifying the user copied several device files on to the system partition in such a way that they remain untouched even after a factory reset.
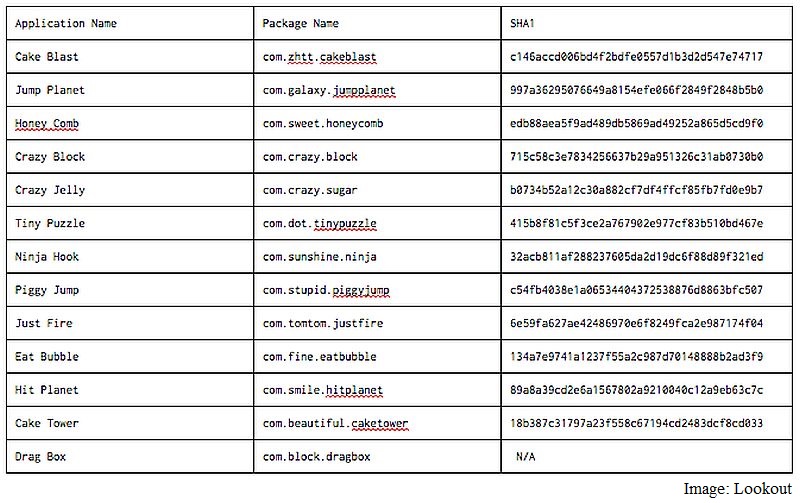
Google officially revealed the application names along with the packagae name and hash codes as mentioned in the image below
Chris Dehghanpoor from Lookout, a mobile security provider identified this intrusion gave an example of what these applications actually do. He quoting the example of HoneyComb said that - the application showed around a million unauthorized downloads and other than boasting of such large number of downloads, it also gave itself positive app reviews - a feature on Google Play to give a boost to the downloads.
It is alarming to see the state of security on Google Play and Android and in words of a researcher It seems likely that over 2-3 months, the malware authors used different names, games, and techniques to see what app they could publish in Play while flying under the radar.
When asked as to how can this malware be removed, Chris Dehghanpoor said, the best way to remove this malware is to perform a re-flash of the Stock ROM (ROM originally supplied by the device manufacturer) since otherwise the malware has the abiliy to survive the factory reset process. The applications are claimed to be written by the developers behind the Brain Test malware family.
In November last year another similar malware family dubbed Shedun was reported to affect Android devices which not only downloaded unwanted applications on the device, but also found a hidden vulnerability in Android OS that made it possible for the malware to find alternate ways of interacting with the device.